- Mar 17
Cross App Access: Securing Enterprise AI Agents & App Integrations
- Daniel Krzyczkowski
For years, enterprises have relied on a simple but brittle pattern for app-to-app communication: static API keys. A developer generates a long-lived credential, stores it in a config file (or worse, checks it into version control), and uses it every time an application needs to access another application's API.
This approach has worked at small scales, but it comes with serious security trade-offs:
Credential sprawl: Keys live in dozens of places like pipelines, environment variables, config files, secrets managers - each one a potential attack surface.
No time limits: A stolen key remains valid until someone notices and rotates it, which could be weeks or months.
Overly broad access: A single API key typically grants the same permissions regardless of context. A key for "write to Salesforce" has the same power whether the request comes from an automated workflow or a rogue agent.
Invisible to compliance: When app A silently accesses app B's data, there's no audit trail connecting that action to a human user or organizational policy.
As enterprises accelerate AI adoption and agent proliferation, these problems become critical. An AI agent running without proper identity controls could become an insider threat, silently exfiltrating data or executing unauthorized actions with nobody the wiser.
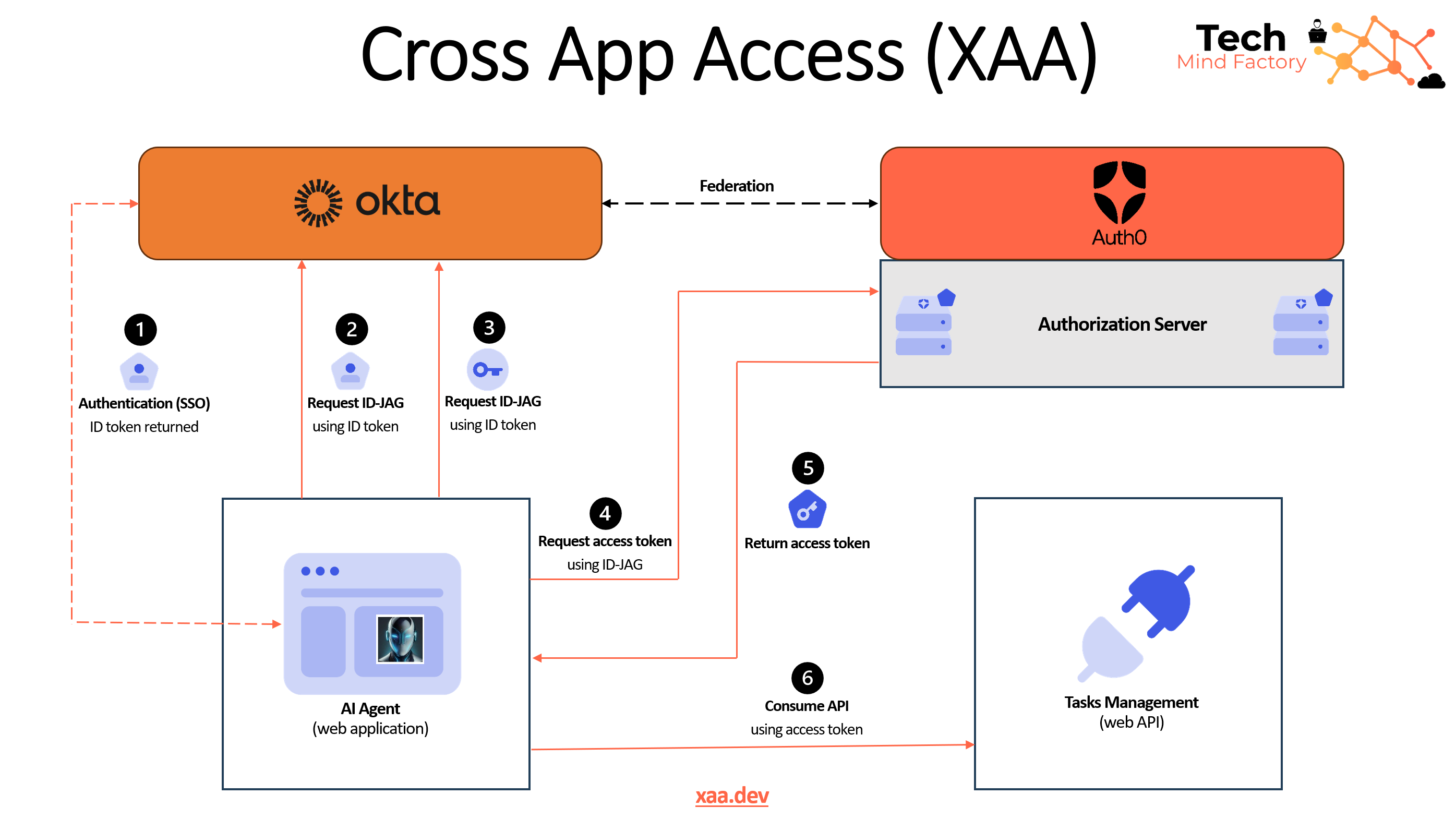
Cross App Access (XAA) Introduction
Cross App Access (XAA), formally known as the Identity Assertion Authorization Grant(ID-JAG), is an extension of OAuth that enables an enterprise identity provider to manage the connection between two applications. In simpler terms, XAA treats app-to-app communication the same way your organization already treats user logins: through a centralized identity provider that decides who gets access to what, and when.
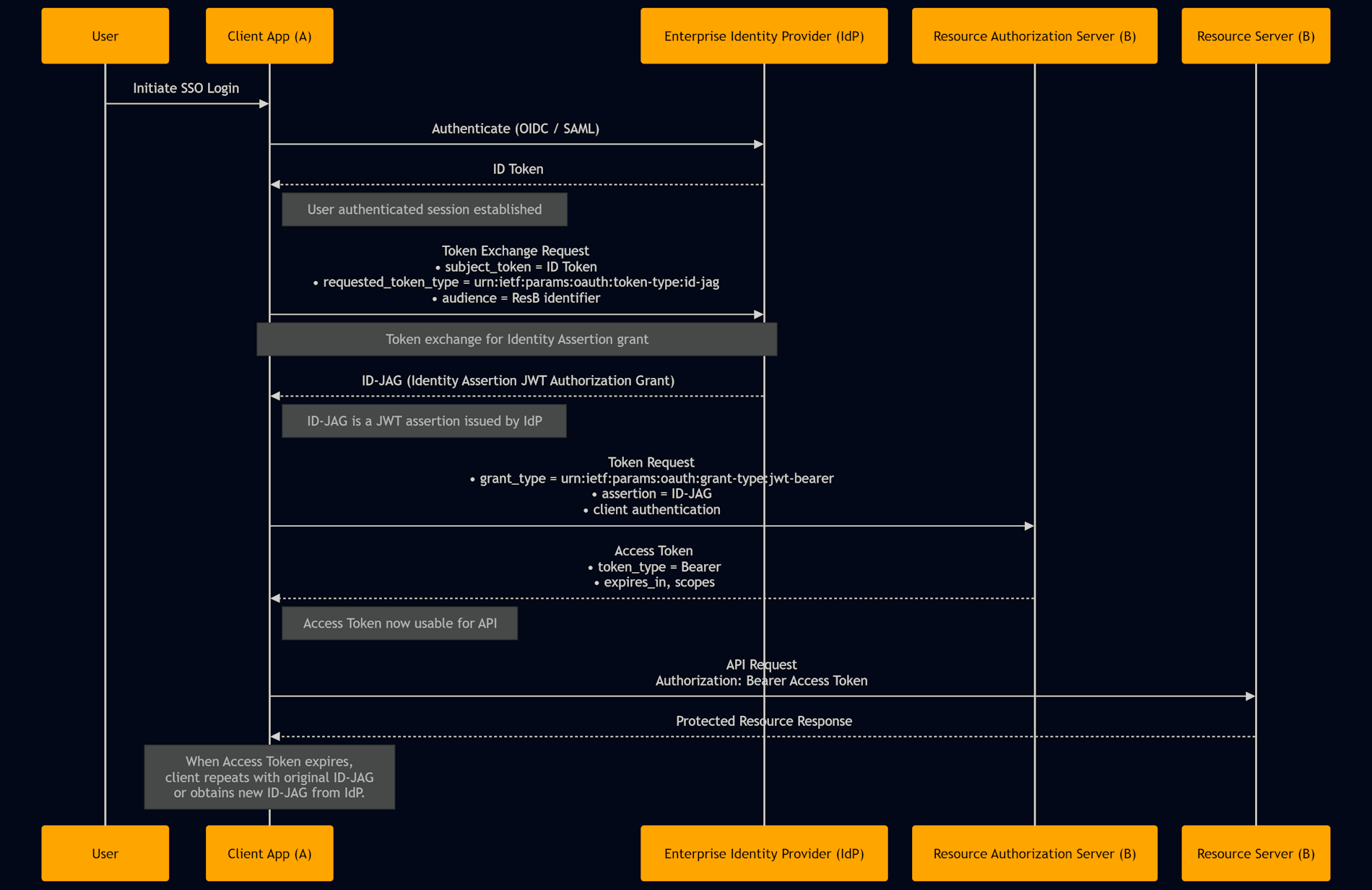
How XAA Works: The Three-Party Flow
XAA involves three key players in every transaction:
Requesting app: The application or agent that needs access (e.g., an AI agent)
Resource app: The application that owns the protected API (e.g., Salesforce, Slack)
Enterprise IdP: The identity provider that acts as the trusted broker (e.g., Okta, Microsoft Entra)

Let's walk through each step:
Step 1: User authentication
A user logs into the requesting app using your enterprise SSO (e.g., Okta, Microsoft Entra). The IdP issues a standard OpenID Connect ID token that proves the user's identity.
Step 2: Token exchange request
When the requesting app needs to access the resource app's API, it doesn't grab a pre-stored API key. Instead, it calls the IdP's token endpoint and asks: "I have this ID token from this user. Can I exchange it for a token that lets me access Salesforce on their behalf?" This is where the magic happens.
Step 3: Policy validation & token issuance
The IdP validates the request and checks the XAA policy defined by the Acme IT Admin. If the XAA policy allows for it, the IdP returns the ID-JAG to the Requesting App. The IdP can enforce fine-grained rules: "This AI agent can access Salesforce, but only to read contact data, not update it" or "This app can talk to Slack, but only during business hours."
Step 4: API access
The Requesting App makes a token request using the ID-JAG to the Resource App (Todo0) Authorization Server. The Resource App Authorization Server validates the ID-JAG using the public key it also uses for its OpenID Connect flow with the IdP. The token is short-lived (often just minutes), scoped to the exact permissions needed, and automatically expires.
Why XAA Changes Everything
For security teams
With ID-JAG/XAA, an AI agent requests tokens through the enterprise IdP, on-demand and not as a persistent or long-lived set of credentials. When the agent needs to access Salesforce, for example, it exchanges its ID token (from when the user authenticated with SSO) for a scoped, short-lived token that permits only the specific capabilities needed for the task at hand. The token expires automatically, the request is logged (traceable back to the user and agent), and IT/InfoSec maintains policy control over which agents can access which resources.
For developers
XAA replaces static API keys and service accounts with short-lived, scoped tokens issued through your enterprise IdP, cutting secret sprawl and blast radius. Built on the Identity Assertion Authorization Grant (ID-JAG) and the OAuth 2.0 JWT Bearer flow, XAA lets one app use an IdP-issued identity assertion to obtain a target-specific access token. No more hunting for lost credentials in Slack messages or accidentally committing secrets to Git.
For enterprises
The IdP becomes the control plane for app-to-app trust, providing central policy, unified audit logs, easy revocation, and consistent enforcement of least privilege. When an agent acts suspiciously, security teams can revoke its access instantly, no hunting through multiple systems for hidden credentials.
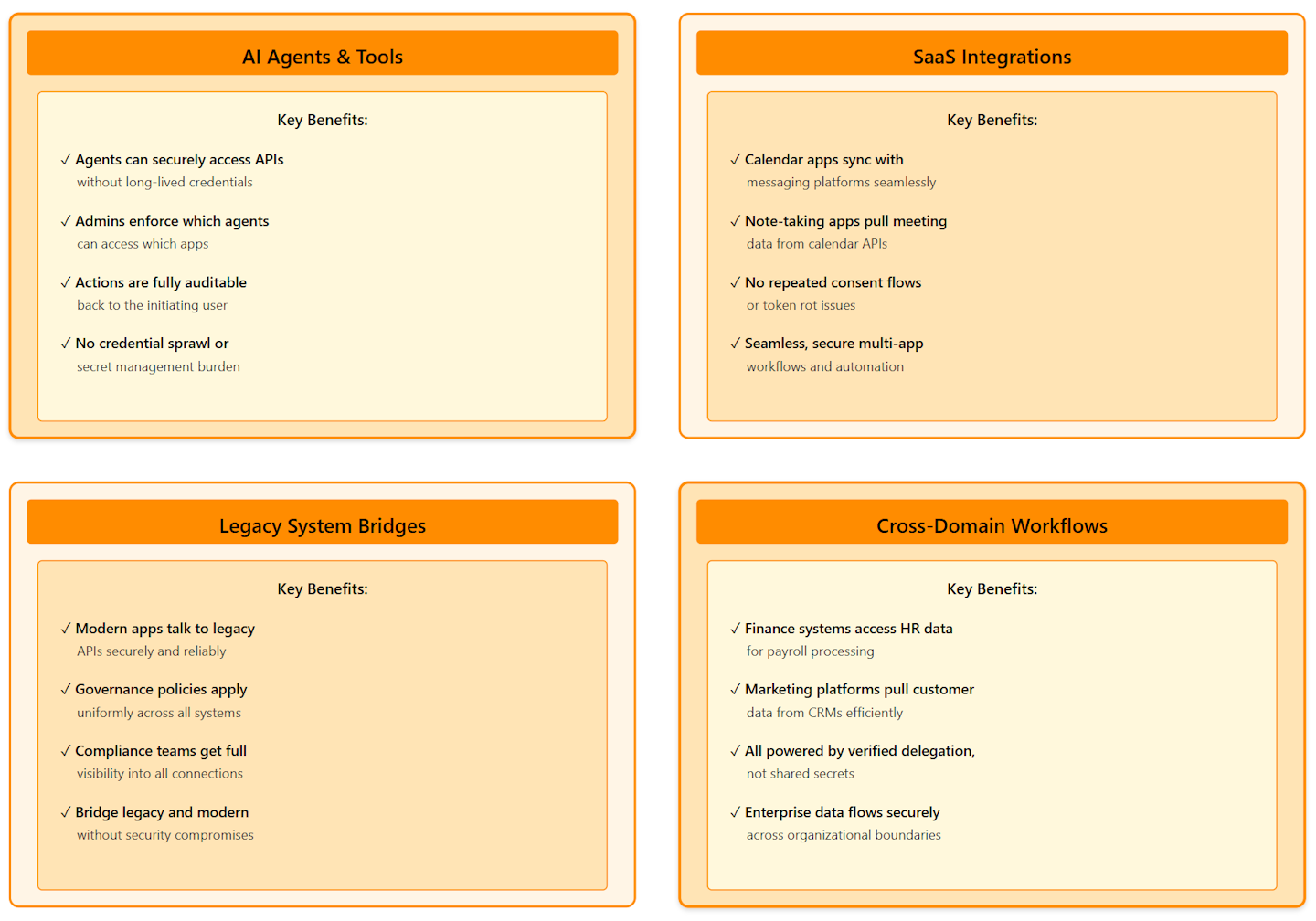
Use Cases
The Path Forward: Industry Adoption
A new open protocol, Cross App Access (XAA) aims to bring agents into existing identity management solutions to govern what kind of data they can access. This isn't a proprietary solution locked to a single vendor, it's an open IETF standard that any IdP can implement.
The XAA landscape is evolving rapidly. ISV applications that implement the protocol (like Box, Salesforce, or AI assistants) integrate Cross App Access into their products, while enterprises enable and configure these capabilities through their existing IdP.
If you want to experiment with XAA before deploying to production, Okta offers a free playground at xaa.dev where you can test the full token-exchange flow in seconds, with no infrastructure setup required.
XAA Support in Leading Platforms
As XAA adoption accelerates, leading identity platforms are integrating native support:
Auth0: Auth0 will support XAA in its APIs and SDKs soon, and Okta will make it a core part of its platform fabric. Auth0 is actively building XAA capabilities to help developers secure AI agents with identity-driven authorization.
Okta: Okta has been the driving force behind XAA standardization and adoption. It's now a core part of the Okta platform, with dedicated developer tooling, documentation, and the xaa.dev playground for experimentation.
Both platforms are committed to supporting XAA as the standard way to govern AI agents and app-to-app integrations at enterprise scale.
Summary
The Cross App Access (XAA) Protocol replaces static API keys with a centralized identity provider approach to app-to-app authentication. Instead of managing long-lived credentials, applications request short-lived, scoped tokens on-demand through the enterprise IdP.
Key benefits:
No credential sprawl or secret management
Centralized policy control and instant revocation
Full audit trails back to the initiating user
Enables secure AI agents, SaaS integrations, and cross-domain workflows