- Aug 14, 2024
Why Verifiable Credentials and Decentralized Identity?
- Daniel Krzyczkowski
Verifiable Credentials and Decentralized Identity are becoming more popular, and there are already some concrete solutions/products available on the market. I think that before even implementing anything concrete, it is important to understand what Verifiable Credentials and what is the purpose of Decentralized Identity.
Centralized Identity Systems

Let's first discuss centralized identity systems that are well known nowadays.
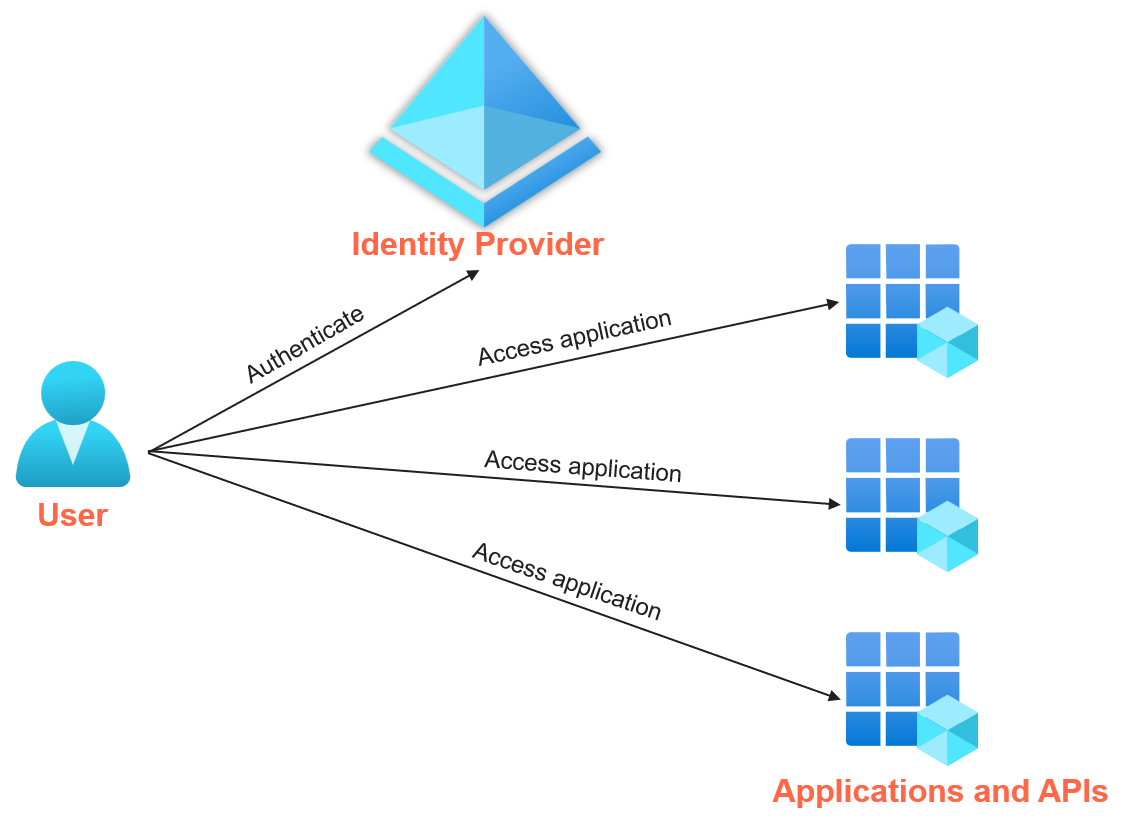
Centralized Identity Management refers to a system where identity data is collected, stored, and managed by a single central authority (also called Identity Provider). Applications and services trust the central identity system component - Identity Provider (IDP).Users use it to authenticate, and get access to resources, and enable transactions.
Examples of Centralized Identity Systems (or Providers) are: Microsoft Entra ID, Okta or KeyCloack. Here is the example of Centralized Identity System:
Centralized Identity Systems - challenges
Centralized Identity Systems have many benefits and are broadly used, however there are also some challenges, here are some of them:
Organizations store vast amounts of personal data from users which leaves users without control over who has access to their personal information.
Limitations when it comes to trust boundary - federations are required.
Centralized Identity Systems introduce a single point of failure.
Data breaches and security risks.
Decentralized Identity Systems

Let's talk about Decentralized Identity Systems now. Decentralized identity allows people to have more control over their digital identities without relying on a central authority or middleman. In these systems, individuals can create, manage, and control their identities using technologies like blockchain, distributed ledgers, and cryptography.
Here are some important facts about Decentralized Identity Systems:
Identity holder have full control and ownership of their data.
Provides user privacy because they can choose which parts of their identity they want to reveal such as showing their age without showing their full name.
There is no need to contact the issuer.
Tamper-proof with cryptography.
Decentralized Identity System - example
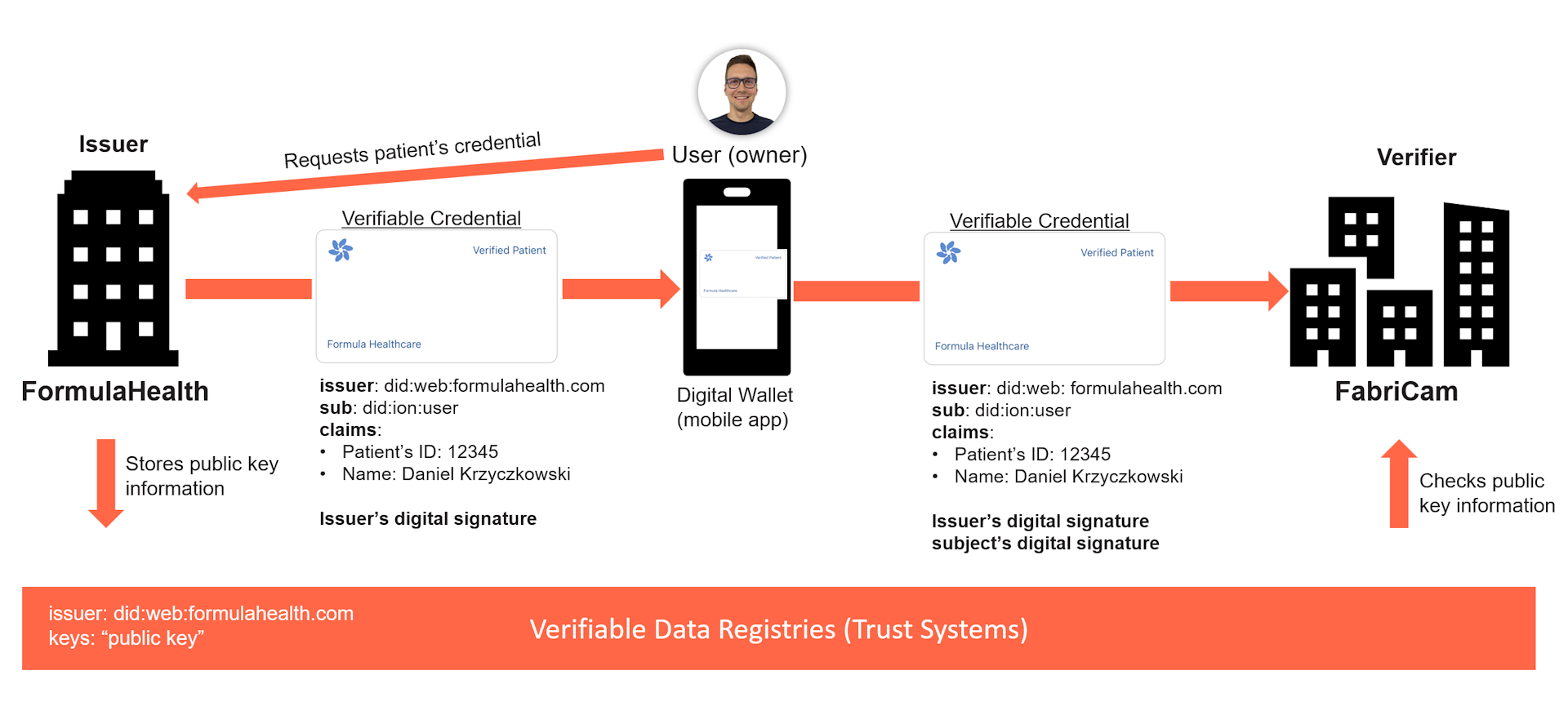
Let's discuss and explain how Decentralized Identity and Verifiable Credentials work. In this scenario we have to healthcare institutions: FormulaHealth and FabriCam:
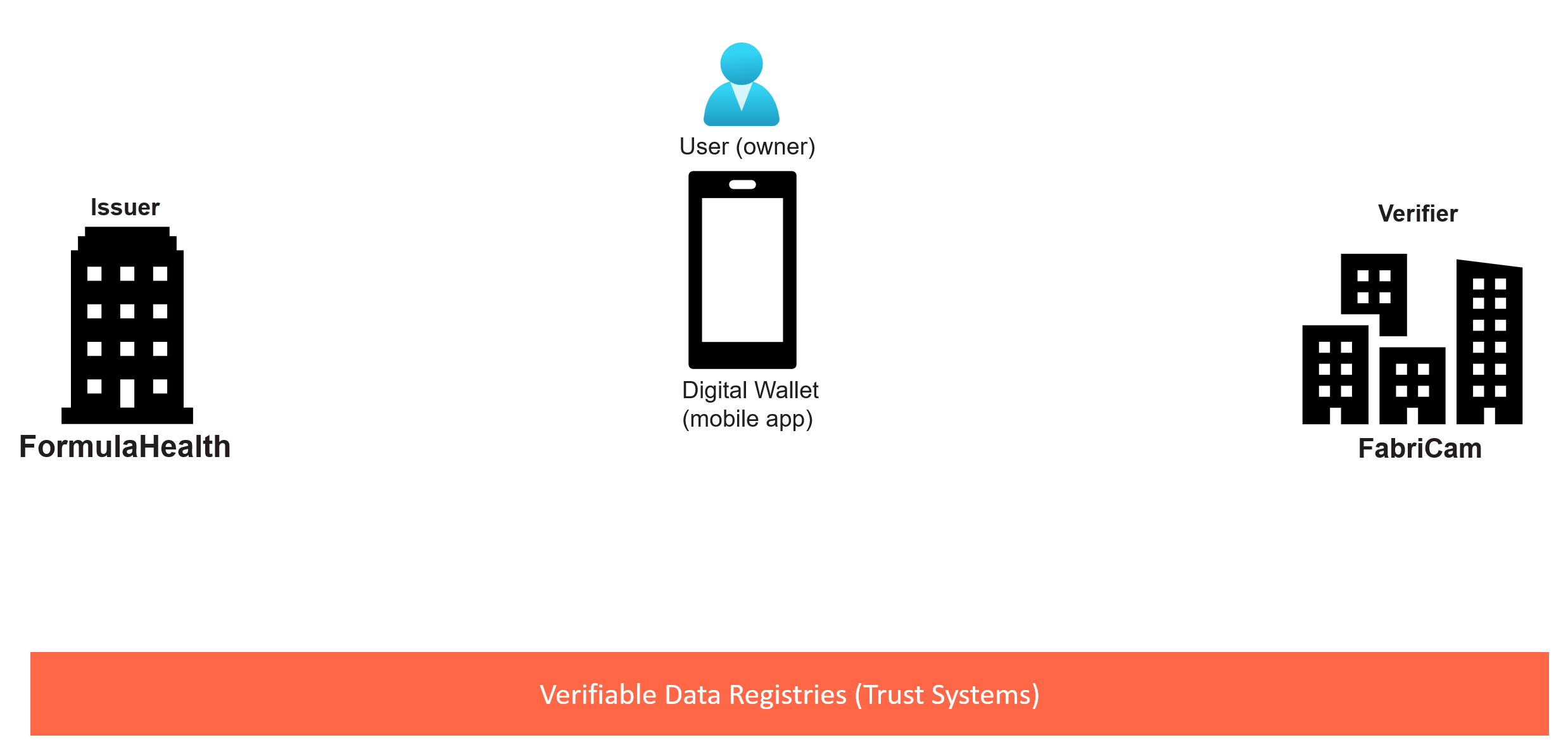
Now let's say that once the user (patient) visit FormulaHealth to do some check-ups, user is issued with Verifiable Credential which lands in the user's digital wallet (mobile application installed on the user's phone).
Next, user (patient) wants to go to another healthcare institution called FabriCam to do some special health tests. Instead of presenting all the required documents, user (patient) can present Verified Patient Verifiable Credential to FabriCam. How does it work underneath?
Patient requests Verifiable Credential by scanning the QR code generated on the screen in the doctor's room.
FormulaHealth is issuing Verfifiable Credential to patient. This credential is signed with the private key of FormulaHealth.
FormulaHealth public key is published through the Verifiable Data Registry (Trust System). Everyone can access and verify public key of FormulaHealth, without contacting it directly.
Next, patient is visiting FabriCam and is asked to present Verified Patient Verifiable Credential. By scanning the QR code with the mobile application (digital wallet) there is presentation request created. User has to agree to present Verifiable Credential to the verifier (in this case FabriCam). Presented Verifiable Credential is signed with the issuer's private key and the user's (subject's) private key.
FabriCam can then verify digital signature of the presented Verifiable Credential looking into the Trust System and extracting the public key of the issuer (FormulaHealth).
Once we understand how it works, it is also important to some components in this architecture.
Decentralized Identity System Components
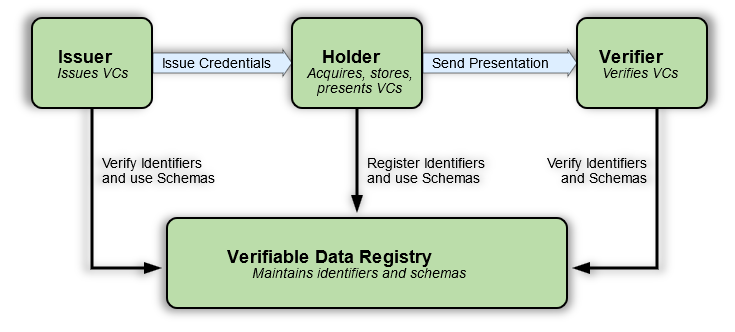
The most important components in the Decentralized Systems architecture are:
Verifiable Credentials
Decentralized Identifiers (DIDs)
DID Documents (DID documents)
Distributed Ledger Technology (Verifiable Data Registry)
Decentralized Identifiers and DID Documents
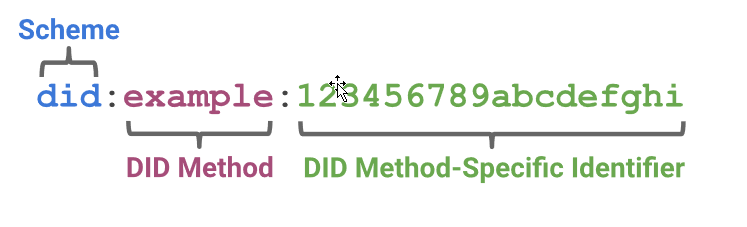
A DID (Decentralized Identifier) is a simple text string consisting of three parts:
The did URI scheme identifier.
The identifier for the DID method.
The DID method-specific identifier.
Decentralized Identifier unique identify the Decentralized Identifier (DID) Document. DID Document is like a digital ID card that helps verify who you are on the internet without needing a central authority (like a government or company) to vouch for you.
Here's a simple breakdown:
1. DID: Think of a DID as a unique username that you create. It’s not tied to your real name or personal details, so it’s private and secure.
2. DID Document: This is a digital file linked to your DID. It contains important information, such as:
Public Keys: They prove that you own the DID and are used during the verification process.
Service Endpoints: These are like contact details, showing for instance the linked domain that you own.
How DID Document is used?
Verification: When someone needs to verify you, they check your DID Document. They can see the public keys and confirm you are who you say you are.
Interactions: You can interact with others securely using your DID, with no need for passwords or third parties to verify you.
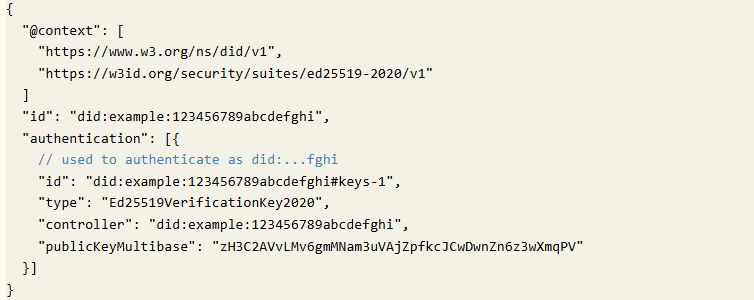
In essence, a DID Document is a way for you to prove your identity and interact online securely and privately, without relying on traditional identity systems.
Verifiable Credentials
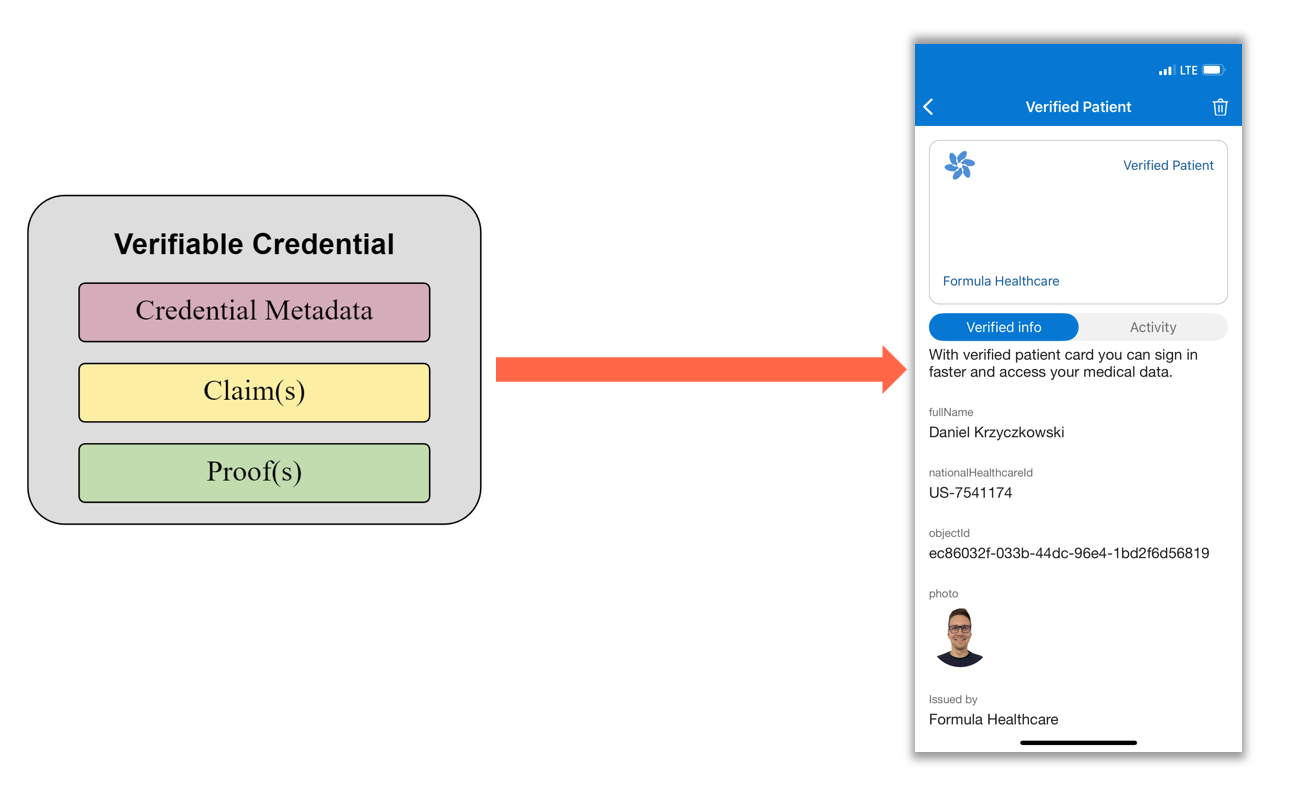
A credential is a set of one or more claims made by the same entity (date of birth, first name, last name).
Credentials might also include an identifier and metadata to describe properties of the credential, such as the issuer, the expiry date and time.
The metadata might be signed by the issuer. A verifiable credential is a set of tamper-evident claims and metadata that cryptographically prove who issued it.
Distributed Ledger Technology (DLT)

Distributed Ledger Technology (DLT) refers to a decentralized database managed by multiple participants across different locations. It records transactions simultaneously in multiple places without needing a central authority and is commonly used in blockchain technologies. DLT uses cryptography. Blockchain is just one specific example of DLT.
Sample scenarios
Account Recovery
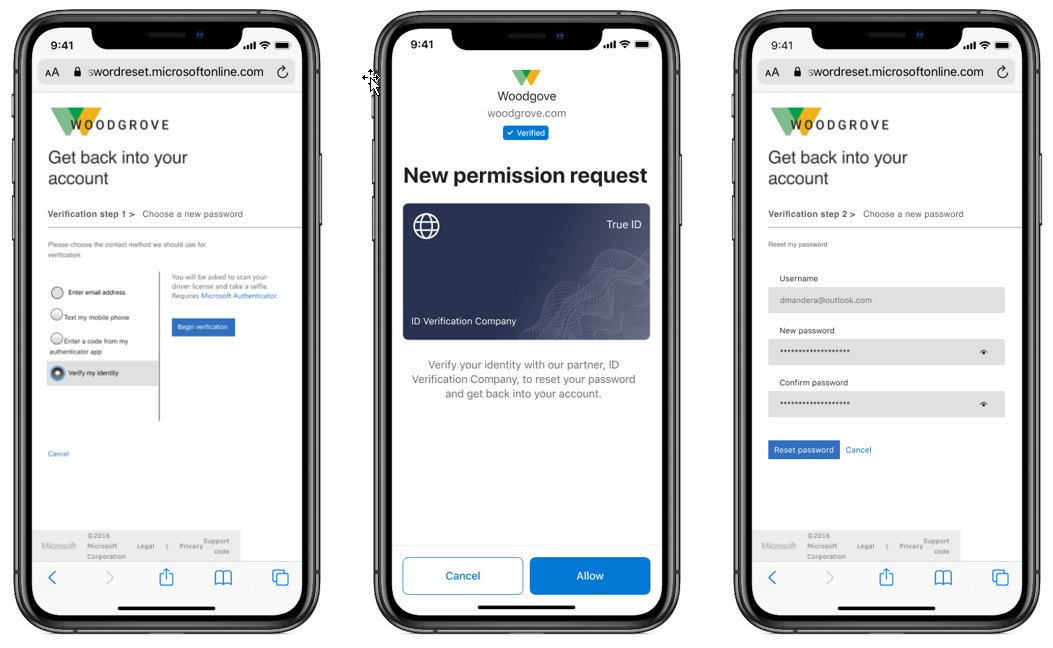
With Verifiable Credentials usage it is possible to reduce support phone calls and security questions with a simpler, more secure process to verify identity.
Car Rental
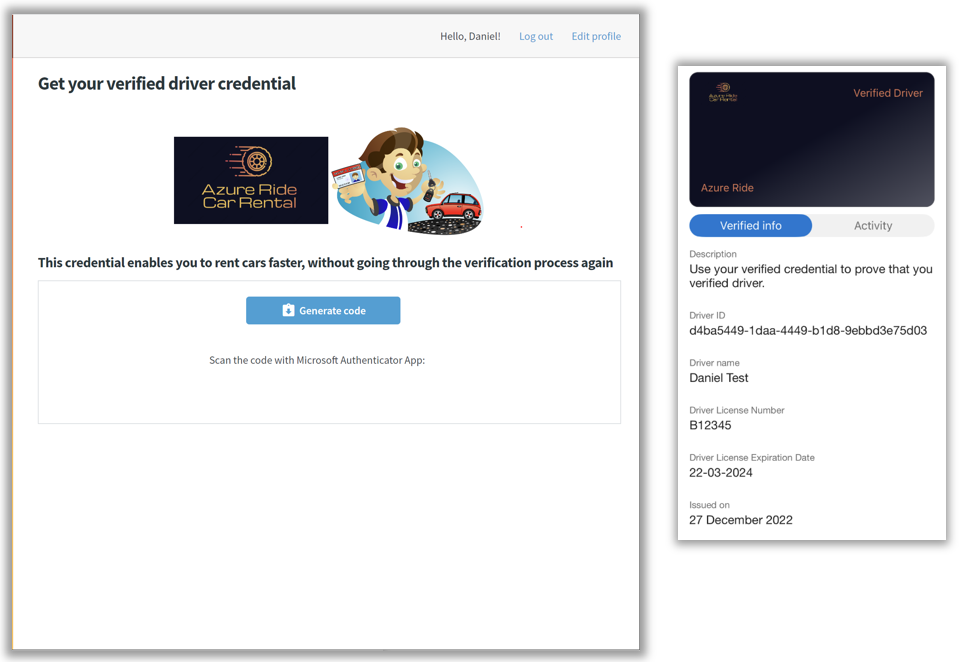
Reduce time to rent a car once the customer was verified. Next time, customer can present Verifiable Credential to access “fast-track” rental section of the web portal.
Are there any standards?

There are standards provided to implement Decentralized Identity Systems. Here are some links if you would like to learn more:
Summary
Transforming physical credentials into digital ones offer the opportunity to make identity verification cheaper, faster, and more secure than current paper-based or semi-online processes. Using physical credentials as-is in a digital world has led to processes such as sending a pdf of a passport attached to an email that are susceptible to weaknesses and vulnerabilities. This is the place where Decentralized Identity and Verifiable Credentials can help.